Key takeaways:
- A DDoS attack aims to overwhelm a site’s server by flooding its system with traffic.
- It’s illegal to launch DDoS attacks.
- There are three major classifications of DDoS attacks: volumetric attacks, protocol attacks, and application layer attacks.
Distributed Denial of Service (DDoS) attacks can overwhelm your website and disrupt your business operation. This can lead to lost customer trust or financial damage, which can be frustrating.
DDoS attacks primary happen through machine and device exploitation.
In this article, you’ll learn what a DDoS attack is, how it works, and how to mitigate it with effective strategies.
What is a DDoS attack?
A DDoS attack is the malicious attempt to flood a website or application with (fake) traffic to crash the site’s server. The goal is to overwhelm the website’s system so real users can’t access it.
There are two categories of Denial-of-Service attacks:
- Denial of Service (DoS) attacks
- Distributed Denial of Service (DDoS) attacks
A DDoS attack is a subcategory of denial-of-service attack. The difference is that a DoS attack comes from a single source, while a DDoS attack comes from a network of compromised devices, hence the term distributed.
In 2020, Amazon Web Services (AWS) experienced a major DDoS attack that is one of the largest ever recorded as of late. GitHub also faced a similar attack in 2018. Beyond outages, DDoS attacks can result in lost revenue and damaged consumer trust. These attacks show that DDoS attacks shouldn’t be taken lightly, and brands need more security systems and website maintenance in place more regularly.
How does a DDoS attack work?
Networks of infected internet-connected devices power these DDoS attacks. These devices go beyond computers, as they often include Internet-of-Things (IoT) devices that include:
- Smart home gadgets
- Routers
- Cameras
Attackers attach malware to these devices and control them remotely.
The network of hijacked devices is called a botnet. Once attackers have successfully set up the botnet, they can instruct the entire network to flood their target website or server with fake traffic at once.
Botnets will flood the site’s system until it slows down and crashes, making it inaccessible for your real (human, non-bot) visitors.
Since the traffic comes from real devices, it’s hard to distinguish an attack from legitimate traffic.
How to identify a DDoS attack?
The obvious sign of DDoS attacks is the sudden slowdown of your website. However, similar issues can happen during spikes in real traffic. So, to differentiate DDoS from legitimate traffic spikes, look for patterns.
Watch out for signs like:
- Large volume of traffic or requests coming from a single IP address or IP range.
- Sudden traffic spike during odd hours of the day.
- A surge of traffic from users of the same device, geolocation, or web browser.
Traffic analytics tools such as Google Analytics can help identify these signs.
What are the common types of DDoS attacks?
Here are the three main classifications of DDoS attacks:
- Volumetric attacks
- Protocol attacks
- Application layer attacks
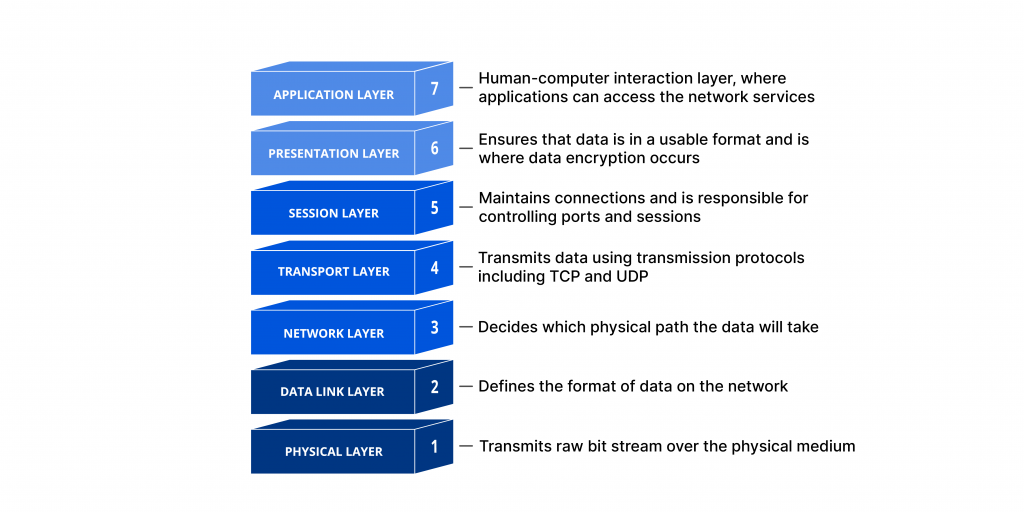
DDoS attacks are classified based on the part of the network they target, often following the model above, also known as Open Systems Interconnection (OSI) model.
Let’s cover the attacks in more detail.
Volumetric attacks
Volumetric DDoS attacks target Layer 3 (Network) and Layer 4 (Transport). It floods the network with heavy traffic, either directly from a botnet or through amplification techniques. The goal is to exhaust all available site bandwidth to make the target network or service inaccessible.
DNS amplification is one of the most common techniques attackers use in this type of attack. In this method, attackers:
- Infect devices with malware and spoof the victim’s IP address.
- Send small DNS queries to open DNS resolvers.
- These resolvers then send large responses to the spoofed IP (the victim), overwhelming the target with traffic.
Protocol attacks
Like volumetric attacks, protocol attacks aim to exploit vulnerabilities in Layer 3 and Layer 4. But instead of clogging the bandwidth, these attacks drain server resources like memory, CPU, or connection limits. The goal is to overwhelm the systems that manage network connections.
A common example of a protocol attack is a SYN flood. When a device wants to connect to a server, it follows a three-step process called a Transmission Control Protocol (TCP) handshake.
In the context of SYN flooding, the attacker sends a large volume of connection requests (SYN packets) using fake IP addresses. The victim’s server then attempts to respond to each request and waits for the final response, which never arrives. As the server holds all these half-open connections, it eventually runs out of space to handle real user connection requests.
Here’s how it works:
- Client’s device sends a request (SYN) to the server.
- The server replies (SYN/ACK).
- Client’s device confirms the connection (ACK).
- Finally, they establish a connection.
Application layer attacks
Application layer DDoS attack targets Layer 7 of the OSI model, the layer where websites and apps interact directly with users. It’s sometimes referred to as a layer 7 DDoS attack.
The attackers pretend to be thousands of real users. It floods a website with fake HTTP requests that look real, all at once. Some HTTP requests that they might do are:
- Reloading a page
- Triggering a search query repeatedly
- Abusing features like carts and login forms
For every fake request, the server has to load multiple files and run database queries to create a web page. Over time, the server gets overwhelmed and eventually crashes.
The worst part? These requests look real, so they’re hard to detect and filter out.
How do I mitigate DDoS attacks?
The biggest challenge in dealing with a DDoS attack is discerning real users and fake traffic. Fortunately, there are many ways to defend against these attacks, including:
- Enabling rate limiting
- Setting up a web application firewall (WAF)
- Diverting traffic using blackhole routing
Let’s take a closer look at how each of these strategies can protect your website from a DDoS attack.
Enabling rate limiting
Have you ever entered the wrong password several times and seen a message like, “too many attempts, try again in 15 minutes”? That’s rate limiting in action.
Rate limiting controls the number of requests a user or device can make within a timeframe. It helps prevent activities like rapid-fire requests from the same IP from happening while still letting real users access your site.
Setting up a web application firewall (WAF)
WAF acts as a protective shield between your website and incoming traffic. It filters out malicious requests before they reach your server.
WAFs are useful for blocking application layer attacks, which are often hard for traditional firewalls to catch. What’s great about WAFs is their ability to analyze traffic patterns, a key factor in identifying and stopping DDoS attacks.
Diverting traffic using blackhole routing
Blackhole routing is a technique of dropping malicious traffic before it reaches your server.
But unlike rate limiting or using firewalls, you can’t set up blackhole routing on your own. Usually, your Internet Service Provider (ISP), hosting provider, or cloud service provider handles this. Ask your provider if they offer this kind of service. Some infrastructure providers like Cloudflare and AWS include this feature as part of their DDoS mitigation service.
The downside of this is that it can also block legitimate users. That’s why blackhole routing is often the last resort. It’s used as a fallback measure during massive attacks.
Check out our cybersecurity guide to find more tips on how to keep your website and visitors safe from cyberthreats.
Maintain a secure website with Network Solutions
DDoS attacks continue to be a serious threat, especially to businesses of all sizes. The problem here goes beyond how to stop traffic; it also involves how to identify real traffic from fake ones. Thankfully, techniques like rate limiting, firewall enabling, and blackhole routing can help mitigate attacks like DDoS.
Want to learn more about website security? Explore more advanced mitigation tips on how to stop a DDoS attack and other online threats through our blogs and knowledge base articles. And while you’re at it, keep your website malware free with Network Solutions’ SiteLock Security and detect threats fast with daily scanning.
Frequently asked questions
Yes. In the US, a DDoS attack is a violation of the Computer Fraud and Abuse Act (CFAA). Those involved in launching the attack may face legal consequences like fines and imprisonment.
Noticing a sudden traffic spike during odd hours of the day is a great sign that you might be under a DDoS attack. Other ways to know if you’re being attacked is by observing patterns like large amount traffic coming from a single IP address, device, geolocation, or web browser.
DDoS attacks vary in length. Some attacks last a few minutes, while others last for several days. The length of the attack differs depending on the attack’s complexity and how the target system response to stop it.