Key takeaways:
- Premium DNS can cut page load time delays that cost businesses up to 7% in conversions.
- Premium DNS is especially beneficial for small businesses that depend on their website for visibility, transactions, or lead generation.
- When selecting a premium DNS service provider, look for options that offer flexibility in managing your DNS settings and provide 24/7 customer support.
Most websites begin with free domain name system (DNS) services from domain registrars or hosting providers. And for a while, that’s often good enough. But as your traffic grows, basic DNS can quickly become a bottleneck for speed, uptime, and security. Case in point: conversions can fall by 7% because of a one-second delay in page load time, and 43% of small businesses have been targeted by cyberattacks, many of which exploit DNS and website vulnerabilities.
At that point, upgrading to a premium DNS would be the most sensible move to protect your online presence and deliver a better experience for your website visitors.
In this article, we’ll explain what a premium DNS is, how it works, and, most importantly, whether it’s worth it for your business.
What is a premium DNS?
Premium DNS is an advanced DNS service designed to improve your website’s performance in terms of speed, reliability, and security. It uses a global network of high-performance DNS servers to offer more than the standard DNS provided by most domain registrars.
Apart from Anycast routing, premium DNS also includes features like SLA-backed uptime guarantees. What’s more, it includes a secondary nameserver as a backup. So, if the primary server goes down, your site will remain accessible. These are, in fact, the same standards that many businesses trust to keep their websites running without disruption.
In a nutshell, a premium DNS gives you:
- Faster DNS resolution, thanks to globally distributed servers
- Higher uptime, backed by service-level agreements (SLAs)
- Built-in protection against threats like Distributed Denial of Service (DDoS) attacks
- Better user experience, especially for global audiences
- Improved stability, even during traffic spikes or server issues
How does premium DNS work?
When someone visits your website, their browser triggers a DNS lookup process to translate your domain name into a numeric IP address. That’s what directs their browser to the correct server. With basic DNS, this request may pass through slower or overused servers. That can lead to delays. Or even temporary outages.
Premium DNS, on the other hand, takes a different approach. It uses a distributed network of servers globally to direct DNS queries to the one nearest to the visitor. This shortens the distance, lowers latency, and helps your website load faster wherever your audience is located.
What’s the difference between basic DNS and premium DNS?
The core difference between basic and premium DNS comes down to scale and expectations. Here’s how the two compare:
| Feature | Basic DNS | Premium DNS |
| Speed & Performance | Basic performance with occasional delays | Fast DNS resolution through global server routing |
| Uptime Guarantee | No guaranteed uptime; may experience outages | SLA-backed uptime (often 99.9%+) for higher reliability |
| Security | Basic protections; vulnerable to spoofing or DDoS attacks | DDoS protection, DNSSEC support, and enhanced fraud prevention |
| DNS Management | Limited interface; basic DNS records editing | Advanced dashboard, DNS templates, record-level control, and bulk updates |
| Support | Community or self-service only | Priority customer service with expert-level assistance |
| Analytics & Reporting | Usually not included | Includes reporting tools and query analytics |
| Authentication | Single login only | Two-factor login authentication and admin access controls |
| Dynamic DNS | Available on some platforms | More robust and stable Dynamic DNS options for changing IP environments |
| Target Market | Suitable for personal or small websites | Ideal for businesses, eCommerce, high-traffic blogs, or service-based websites |
What are the benefits of a premium DNS?
Is premium DNS worth it? That actually depends on how important speed, uptime, and security are to your website.
Below are the advantages you’ll get with a premium DNS service:
- Faster performance for global users
- Stronger protection against online threats
- More stability, less downtime
- Better support and control
- Better experience for your users (and for search engines)
Faster performance for global users
A premium DNS service connects your domain to a global network of strategically placed servers. When someone visits your site, the system routes their request to the closest server. As such, your pages load faster, no matter where they are.
This setup reduces latency for sites with growing traffic and helps prevent slowdowns during peak hours. That’s something basic DNS setups can’t always keep up with.
Stronger protection against online threats
With premium DNS, you get built-in DDoS protection, Domain Name System Security Extensions (DNSSEC) support, and enhanced fraud prevention, which collectively strengthen your website’s defenses. These added security features contribute to the overall DNS security for your website.
More stability, less downtime
Many premium DNS providers offer 99.9% or higher uptime guarantees, backed by service-level agreements.
Even more so, your site remains reachable even if a server crashes or an outage occurs in one region. That’s because premium DNS uses Anycast routing and global redundancy to keep things running behind the scenes.
Better support and control
Managing DNS shouldn’t require a support ticket for every change. Thankfully, premium DNS services typically come with easy-to-use dashboards, DNS templates, and options for bulk updates. That’s especially helpful if you’re running multiple domains or need to make quick changes.
You also get access to expert support, often 24/7, so you’re not left scrambling when something breaks.
Better experience for your users (and for search engines)
Faster resolution times and fewer interruptions are just one of the many benefits of premium DNS. It improves the experience for your users and enhances your search rankings. Search engines like Google factor in site speed and uptime when evaluating websites, so investing in performance pays off in visibility too.
Do you really need a premium DNS?
If your website drives sales, handles customer data, or needs to stay online 24/7, then yes, premium DNS is worth serious consideration. Still, not every site requires this level of support. That said, use the checklist below to see if your website needs to switch to a premium DNS service.
You need premium DNS if:
- You run an eCommerce store or online business that depends on 24/7 availability
- Your site experiences frequent traffic spikes or serves a global audience
- You’ve dealt with slow page loads or downtime in the past
- You need protection against DDoS attacks or other DNS-related threats
- You want faster DNS resolution to improve user satisfaction and SEO
- You manage multiple domains and need more administrative control over DNS settings
- You want guaranteed uptime backed by SLAs
- You prefer having dedicated customer support for major issues
- You collect sensitive data or handle customer logins and transactions
- You simply can’t afford disruptions that could impact revenue or reputation
If you checked even a few of these, investing in a premium DNS service is likely worth it.
How to set up premium DNS with Network Solutions
Network Solutions, like many domain registrars, offers premium DNS as an optional add-on to improve your domain’s speed, security, and uptime. Here’s how to add it to your domain:
- Log in to your Network Solutions account.
- From the main dashboard, click on the Domains tab.
- Click the domain name you want to add premium DNS to.
- Scroll down and navigate to the Advanced Tools section.
- Then, click Add Premium DNS.
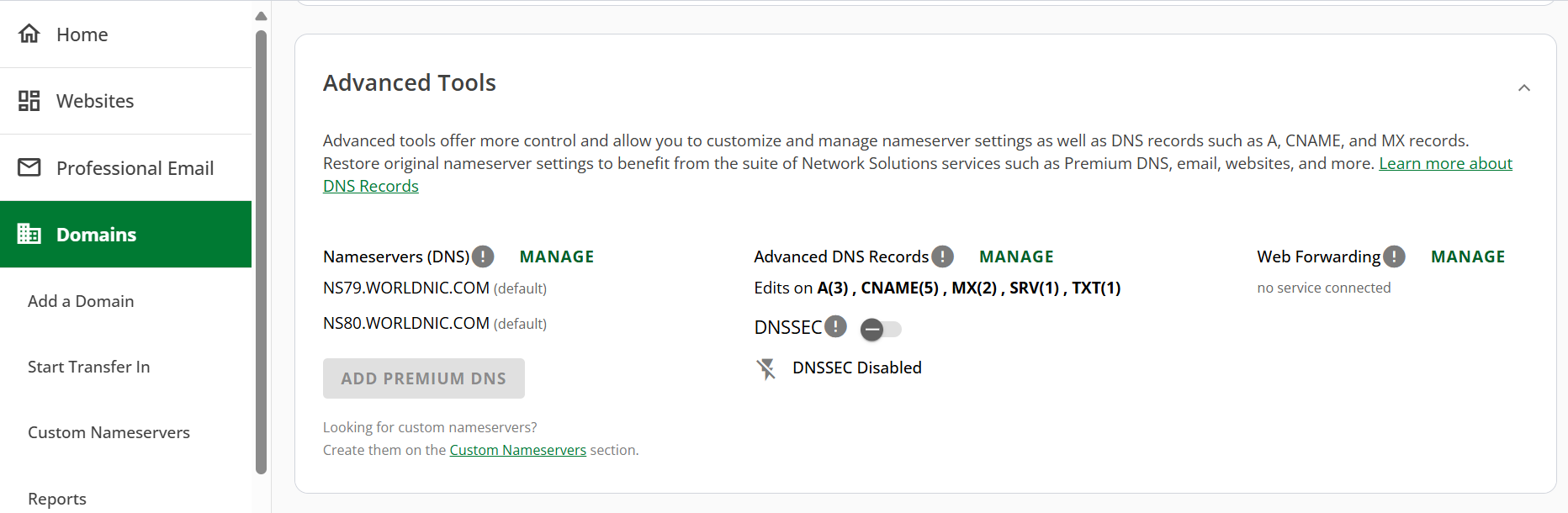
- Once Premium DNS is active, review your DNS records to make sure everything is configured properly. If needed, update or add new records to the DNS management dashboard.
- After the setup, test your website to ensure everything is working smoothly. You can use DNS monitoring tools, like Pingdom, UptimeRobot, or DNSstuff, to check if your DNS queries are being resolved faster and if your site loads more quickly.
Tips for choosing a premium DNS provider
Before you go shopping around for premium DNS providers, here are some of the things you should consider:
- Look for a DNS hosting provider with a global network of DNS servers.
- Pick a provider with a solid uptime guarantee (99.9% or higher) to keep your site online, even during high traffic or server issues.
- Make sure the provider offers strong DDoS protection and DNSSEC support to keep your site safe from cyber threats and attacks.
- Go with a provider that offers quick, 24/7 customer support, especially for DNS troubleshooting or setup.
- Pick a premium DNS provider with an easy-to-navigate dashboard to manage DNS settings without needing technical expertise.
- Compare pricing and check if they offer scalable plans, bulk discounts, or advanced features that fit your needs.
- Look for added benefits like Dynamic DNS, traffic balancing, and analytics to boost your website’s performance.
Why you should choose Network Solutions’ premium DNS service
Network Solutions offers premium DNS as part of our domain registration services. This service primarily provides protection against DNS-based threats like hackers and DDoS attacks.
Even better, our premium DNS offers additional benefits. For instance, the service automatically detects and directs site visitors to the closest of 21 global DNS servers. Plus, it also delivers peak performance levels with maximized website availability and a more improved user experience with 100% uptime.
With Network Solutions’ premium DNS service, it’s easier to:
- Minimize website errors and query failures
- Boost load times and website resolution speed
- Secure sensitive data from hackers
- Prevent attackers from redirecting your site to steal customer information
If you’re looking to boost your website’s security and traffic, premium DNS is the way to go. With Network Solutions, you can keep your site safe from hackers while ensuring maximum uptime. Our global servers, coupled with 100% uptime and robust protection, make our Premium DNS an ideal solution for businesses of all sizes. It’s yet another way to ensure your business stays safe and runs seamlessly online.
Protect your website with a premium DNS
If your website supports your business, every second of uptime and every layer of protection counts. Fortunately, premium DNS provides just that: faster load times, improved security, and greater reliability.
For small businesses that depend on a stable online presence, a premium DNS is indeed a smart choice. Plus, when you combine it with additional features like Domain Privacy + Protection and Domain Management, you’re making sure your site stays secure, runs smoothly, and is ready for growth.
Frequently asked questions
The primary purpose of DNS is to translate human-readable domain names (like yourbusiness.com) into IP addresses that computers can understand. This lets users access websites using easy-to-remember names rather than complicated numeric addresses.
Premium DNS makes websites faster, more secure, and more reliable by using a global network of servers. If you run a business or eCommerce site that can’t afford downtime or slow load times, Premium DNS gives you the performance boost and protection you need.
Free DNS is generally safe for basic use, but it often lacks advanced security features like DDoS protection and encryption. For small, personal websites with low traffic, free DNS services may suffice. However, for business sites or those handling sensitive information, a paid DNS service provides better security and performance.
The cost of Premium DNS varies depending on the provider, but it typically comes with monthly or annual plans. Prices generally range from $10 to $30 per year, depending on the level of service and the features included.
Premium DNS is ideal for websites that require enhanced performance, security, or advanced features, such as high-traffic websites, eCommerce sites, global businesses, websites needing better security, and sites with advanced DNS needs.
Yes, if your site relies on uptime, speed, and handles user data. It’s important for business and eCommerce websites.
Absolutely. Poor DNS performance can delay or fail to resolve website access, which leads to downtime.