Key takeaways
- Cipher suites define how encryption, authentication, and data protection work in secure connections.
- Modern cipher suites offer stronger security and faster performance than outdated ones.
- Keeping your cipher suite settings updated is essential for protecting your website and users.
The security of a secure website or online service depends on SSL/TLS encryption. But a cipher suite is the one that determines how strong and safe that encryption is.
In this article, we’ll break down in detail what a cipher suite is, how it works in a TLS handshake, the difference between modern and outdated suites, and how to configure them securely.
What is a cipher suite?
A cipher suite is a standardized set of cryptographic algorithms that determine how secure communication is established over the internet. It governs four key tasks: key exchange, authentication, encryption, and data integrity. Cipher suites are used in security protocols like Transport Layer Security (TLS) and Secure Socket Layer (SSL) to protect HTTPS connections.
Let’s look at the cipher suite as a secret code that two agents agree on before sharing confidential information. Imagine two spies meeting. Before they exchange secrets, they agree on a special handshake to recognize each other. The internet does something similar when your browser connects to a website. They choose a cipher suite, which is a set of rules that tell them how to encrypt messages (so no one else can read them), how to prove they are who they say they are, and how to make sure the messages aren’t tampered with. Once this is set, they can communicate securely, even if someone is trying to eavesdrop.
Behind the scenes, cipher suites help keep your information private, authentic, and untouched, powering the security of every https:// connection on the internet.
Why cipher suites matter?
Cipher suites matter to your website’s security and your users’ trust because:
- They protect your users’ sensitive data. Cipher suites use encryption to ensure that personal details, login credentials, and payment information stay hidden from hackers during transmission.
- They verify trust and authenticity. Through authentication algorithms, cipher suites confirm that users are actually connecting to your real website, not a fake or malicious copy.
- They maintain data integrity. Even if encrypted, data can still be tampered with. However, cipher suites include message authentication mechanisms that detect and block unauthorized changes.
- They impact site performance. Modern cipher suites are designed for speed, reducing the time it takes to establish secure connections and improving load times, especially on mobile devices.
- They support broad compatibility. Well-configured suites ensure your website can connect securely with a wide range of browsers, devices and operating systems without errors or handshake failures.
- They help meet compliance standards. Regulations such as general data protection regulation (GDPR) and PCI DSS require strong encryption, and cipher suites play a direct role in meeting these technical security requirements.
- They prevent known vulnerabilities. Outdated cipher suites can leave your site vulnerable to serious exploits, such as POODLE, BEAST and Heartbleed. These are threats that modern cipher suites are designed to block.
How do cipher suites work in a TLS handshake
When you visit a secure website with HTTPS, your browser and the website’s browser establish a secure connection through the SSL/TLS handshake.
Here’s how it works:
- Client hello. This is where the client sends a list of supported cipher suites to the server.
- Server hello. The web server chooses the most secure cipher suites supported by both client and server.
- Key exchange. The key exchange algorithm securely shares the encryption keys.
- Encryption. Data is encrypted using the selected encryption algorithm.
- Authentication and integrity. Authentication algorithms validate the connection, while hashing ensures data integrity.
This process ensures that the handshake is quick, safe, and resistant to threats such as data breaches.
The 4 core components of a cipher suite
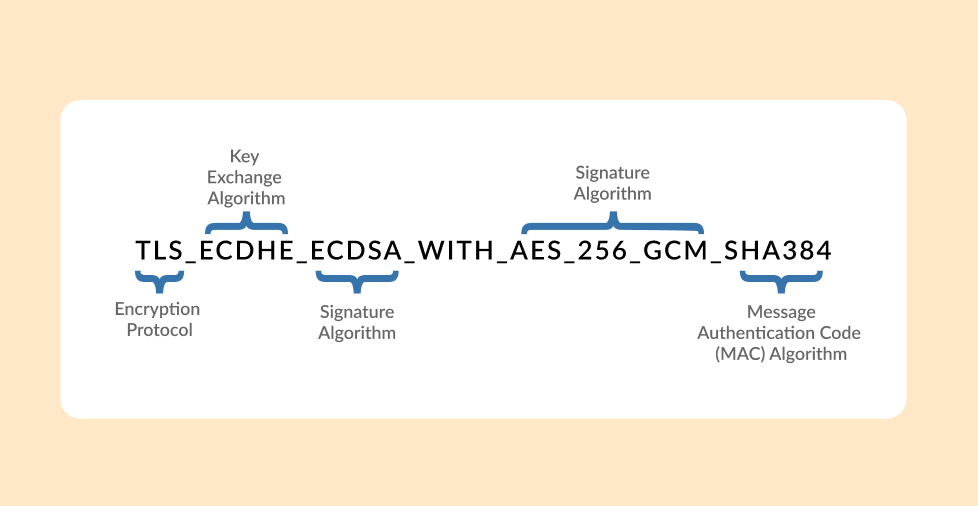
Every cipher suite is made up of several cryptographic algorithms, each with a specific job. While the structure may vary slightly between TLS versions, most modern cipher suites consist of the following components:
- Key exchange algorithms
- Authentication algorithms
- Bulk data encryption algorithms
- Message authentication code (MAC) algorithms
1. Key exchange algorithms
A key exchange algorithm is a method that creates and exchanges secret keys between two or more parties. This process is performed during the SSL/TLS handshake to ensure data confidentiality during file transfers.
In the example given, the key exchange algorithm was represented by Elliptic Curve Diffie Hellman Ephemeral (ECDHE), which outlines how the client and the server will exchange the keys. The “ephemeral” part means temporary keys are generated for each session, which enhances security by providing Perfect Forward Secrecy (PFS)—ensuring that past communications remain secure even if long-term keys are later compromised.
Other common algorithms include:
- Rivest–Shamir–Adleman (RSA). The RSA algorithm is previously used for both key exchange and authentication. However, it’s no longer recommended for key exchange in modern TLS due to lack of forward secrecy.
- Diffie-Hellman (DH). Allows two parties to jointly establish a shared secret over an insecure channel.
- Elliptic Curve Diffie-Hellman (ECDH). A more efficient variant of DH using elliptic curve cryptography, but without the “ephemeral” key component, it doesn’t provide forward secrecy.
Compared to other algorithms, ECDHE is much faster and offers stronger security. While ECDHE and ECDH are nearly similar, ECDHE gives you the forward secrecy, while ECDH does not.
ECDHE is the only one compatible with the PFS feature, which enables short-term, private key exchanges between clients and servers in SSL/TLS.
2. Authentication algorithms
Authentication algorithms are a set of rules used by a computer system to verify the identity of an entity. It checks if the entity that wants to connect to your website matches the password or unique code it gives before allowing access.
In the example provided, the authentication algorithm is represented by the Elliptic Curve Digital Algorithm (ECDSA). This digital signature shows the certificate type and helps the client verify that the website’s SSL is authentic.
Aside from ECDSA, here are some common algorithms used for authentication:
- Digital signature algorithm (DSA). This method uses a complex mathematical problem to create digital signatures. It’s like a unique fingerprint that proves the authenticity of a digital document or message.
- RSA. This algorithm is based on the difficulty of breaking down large numbers into their prime factors. It’s like a strong lock that’s almost impossible to crack, making it a popular choice for secure communication.
3. Bulk data encryption algorithms
Bulk encryption is a method where combined transmissions from several data streams are encrypted together. This method encrypts large amounts of data, making it almost impossible for anyone without a proper decryption algorithm to read.
This cipher ensures that the data transmission between the client and server is secure from any data breach. AES_256_GCM is used to represent it in the example.
Advanced encryption standard (AES) is the method commonly used for bulk data encryption due to its flexibility and compatibility across platforms. However, aside from AES, there are other algorithms that can be used depending on specific security requirements and performance needs.
Symmetric-key algorithms:
- Triple data encryption standard (3DES). It’s a more secure version compared to the older DES algorithm, but it’s slower compared to AES.
- Blowfish. This is a fast and secure algorithm that is often used in software applications.
- Twofish. This is also another strong algorithm that can be used as an alternative to AES.
- Camellia. This is another strong and efficient key block cipher that provides a high level of security while suitable for various applications.
4. Message authentication code (MAC) algorithms
A message authentication code (MAC) is used to verify both the integrity and authenticity of a message. It’s a short piece of data generated by a cryptographic function that takes a message and secret key as input.
The MAC authentication code ensures data integrity, confirming that the data wasn’t tampered with during transmission. It’s represented by the SHA384 in the example above.
Common MAC algorithms:
- Hash-based message authentication code (HMAC). This is a popular algorithm that utilizes a cryptographic hash function like SHA-256.
- Cipher-based message authentication code (CMAC). This MAC algorithm is based on a block cipher like AES.
- Poly1305. This is a modern MAC algorithm that is known for its speed and security.
On the other hand, the newer TLS version TLS 1.3 cipher suite only uses two ciphers: the bulk data encryption and MAC algorithm.
This is a more secure version than TLS 1.2 because it shortens the handshake process, as there’s no need to display the type of key exchange algorithm and authentication algorithm. It’s because TLS 1.3 only accepts the Ephemeral Diffie-Hellman method of key exchange.
Modern vs. deprecated cipher suites
Modern Cipher Suites are security systems that use the strongest encryption methods available and work with newer protocols like TLS 1.3 and secure TLS 1.2 setups. A key feature of this system is PFS. Even if hackers steal your main security key later, they can’t decrypt your old conversations. These cipher suites are fast and protect against all known attacks.
Deprecated Cipher Suites, on the other hand, use outdated encryption that modern computers can easily break or that has known weaknesses. They’re often tied to old, insecure protocols like SSL 3.0 or early TLS versions. Using these old cipher suites leaves you vulnerable to attacks. Hackers can force your connection to “downgrade” to these weaker security methods, making your data easy to steal.
TLS 1.2 vs TLS 1.3 cipher suites
We’ve mentioned two TLS versions earlier: TLS 1.2 and TLS 1.3. Let’s look at what sets them apart.
| Feature | TLS 1.2 | TLS 1.3 |
| Cipher suite options | 30+ options, highly configurable | Only 5 streamlined choices |
| Key exchange & authentication | Built into the cipher suite | Handled separately from the cipher suite |
| Handshake speed | Slower – multiple round trips | Faster – just one round trip |
| Security approach | Includes some legacy algorithms | Removes outdated and risky ciphers |
| Forward secrecy | Optional | Required by default |
| AEAD encryption (like AES-GCM) | Optional | Mandatory |
Examples of Cipher Suites in TLS 1.2 and TLS 1.3
Recommended TLS 1.2 Cipher Suites:
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256,
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256,
TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256
TLS 1.3 Cipher Suites (just 5 options):
TLS_AES_256_GCM_SHA384,
TLS_AES_128_GCM_SHA256,
TLS_CHACHA20_POLY1305_SHA256,
TLS_AES_128_CCM_SHA256,
TLS_AES_128_CCM_8_SHA256
What are some best practices for keeping cipher suites secure?
Here are a few best practices you can do to keep your cipher suites secure:
- Use TLS 1.3 when possible
- Regularly audit cipher suite configurations
- Keep server and client software updated
- Test using SSL Labs, Qualys, BrowserLeaks
Use TLS 1.3 when possible
TLS 1.3 offers significant improvements over older versions, including faster handshakes, built-in forward secrecy, and the removal of insecure legacy ciphers. If your hosting environment supports it, make TLS 1.3 your default protocol for all encrypted connections. It simplifies configuration and raises your baseline security instantly.
Regularly audit cipher suite configurations
Security standards evolve constantly—what was considered “strong” a few years ago might be vulnerable today. Schedule regular reviews of your server’s supported cipher suites and remove any that rely on outdated or deprecated algorithms like RC4, 3DES, or SHA-1. This also helps with compliance, especially under PCI DSS or GDPR.
Keep server and client software updated
Your TLS configuration is only as secure as the software it runs on. Ensure your web server software (like Apache, NGINX, or IIS) and any relevant client libraries are kept up to date. Updates often include important patches for cryptographic vulnerabilities and add support for newer, more efficient cipher suites.
Test using SSL Labs, Qualys, BrowserLeaks
Tools like SSL Labs, Qualys SSL Test, and BrowserLeaks.com provide free, in-depth diagnostics of your SSL/TLS configuration. These tools will score your site’s cipher suite strength, highlight weak or obsolete settings, and offer actionable insights for improving security.
Secure your website with modern cipher suites today
In summary, cipher suites are the backbone of secure online communication. They shield user data, ensure compliance, and build customer trust. By updating your configurations and following the best practices, you can protect your website from vulnerabilities and provide a safe, trustworthy experience for your customers.
Ready to optimize your website security? Take the first step with Network Solutions and explore more ways to protect your site with our robust security solutions such as SSL certificates and SiteLock.
Frequently asked questions
A cipher is a single encryption algorithm, while a cipher suite is a complete package of multiple security components (encryption, authentication, key exchange, and hashing algorithms) that work together to secure a connection.
You can test these using tools like SSL Labs, Qualys SSL Test, or BrowserLeaks. These tools show which cipher suites are active during a connection.
Both are secure, but they’re optimized for different use cases. AES-256 is faster on hardware with built-in acceleration, while ChaCha20 performs better on mobile and lower-powered devices. The right choice depends on your environment.
Yes, but TLS 1.3 uses a simplified approach with fewer, more secure cipher suites and removes weaker algorithms that were available in earlier TLS versions.
For TLS 1.3: TLS_AES_256_GCM_SHA384 and TLS_CHACHA20_POLY1305_SHA256 are considered the most secure. For TLS 1.2: ECDHE-RSA-AES256-GCM-SHA384 or ECDHE-ECDSA-AES256-GCM-SHA384 are top choices.